This third comprehensive chronology of international terrorist attacks covers 2016, during which the Islamic State suffered several battlefield reversals yet continued its operations as the most active, well-financed and well-armed terrorist group worldwide.
Domestic and international incidents around the world are covered and several trends are observed. A new format and organization allows readers to quickly access the most up-to-date information and make regional comparisons.
Review
“Superior…highly recommended”―ARBA.
- Title : Terrorism Worldwide, 2016
- Authors : Edward Mickolus
- Publisher : McFarland
- Publication Date : February 14, 2018
- Language : English
- Paperback : 260 pages
- ISBN-10 : 1476671559
- ISBN-13 : 978-1476671550
- Item Weight : 12.8 ounces
- Dimensions : 7 x 0.52 x 10 inches
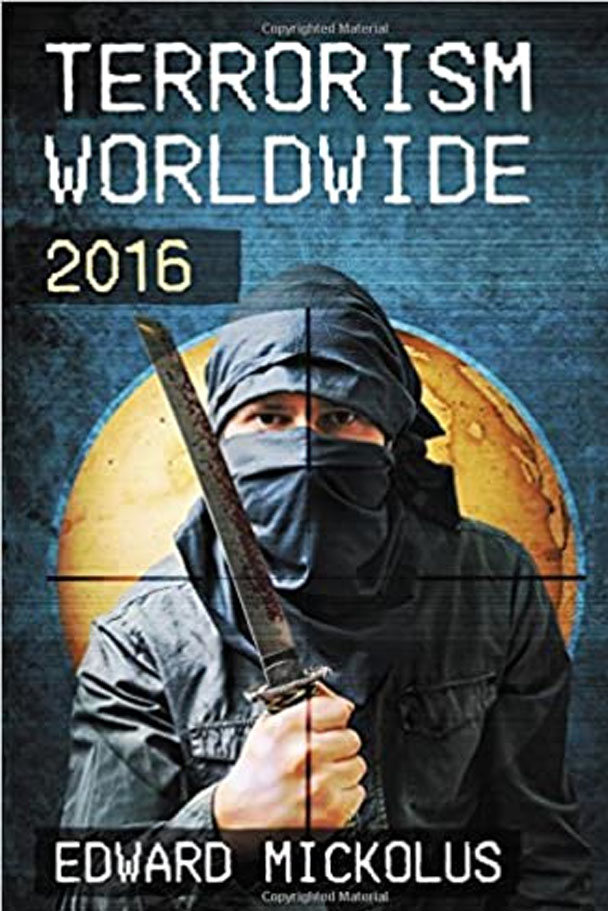
Table of Contents
Introduction
Worldwide
Africa
Asia
Australia/Oceania
Europe
Latin America
Middle East
North America
Updates of pre-2016 incidents
Index of Terrorist and Other Groups and Organizations
Bibliography
Introduction
Although international terrorism in 2016 was not only the work of the Islamic State (IS), a noteworthy amount of attacks were attributed to IS and its affiliates. Because of its international spread and radically decentralized method of operations-by-inspiration, a quick scan of this book’s Index demonstrates that few days go by without an attack by someone declaring fealty to, if not membership in, some form of IS.
The earlier al-Qaeda in the Arabian Peninsula call to use whatever you have at hand was adopted by those inspired by the Islamic State in Iraq and Syria (ISIS). The use of edged weapons—much harder to control than firearms, especially in Israel and Bangladesh, and heavily-laden trucks offered a new repertoire to terrorists.
The Middle East
The terrorist environment was dominated by the struggle to retake territory from ISIS. IHS Jane’s Terrorism and Insurgency Center reported that ISIS lost nearly a quarter of its territory in Iraq and Syria. Its capital of Raqqa, Syria, remained in ISIS hands, but oil revenues were slowed by its geographic losses. This did not stop the proliferation of affiliates and like-minded lone wolves from conducting attacks throughout the Middle East, Asia, North America, Africa, and Europe.
Palestinian grievances broke out into a skein of gun, knife, and vehicle attacks against security forces and civilians in Israel, the Gaza Strip, and other occupied territories.
Latin America
The best news in the region was the peace treaty between the government of Colombia and the country’s largest rebel group, the FARC. Although the initial pact lost by a razor-thin margin in a referendum, the second draft ended a half century of strife in which more than 200,000 people were killed. The country’s second-largest group, the National Liberation Army (ELN), decided to try the peace route as well, although as of this writing, no talks had been held.
The Obama Administration’s efforts to uphold the President’s campaign promise to close the Guantanamo Bay military prison for terrorist detainees saw a fire-sale effort to transfer prisoners to other countries. As of the dawn of the Trump Administration, 41 detainees remained, although the Trump campaign promised to restock the facility with other “bad dudes”. Recidivism by Gitmo alumni—at least a dozen were suspected of returning to the battlefield—added to the headaches that recipient countries, in particular Uruguay, experienced with the former detainees.
Africa
Although government troops, sometimes assisted by the African Union or Western allies, were able to take back large chunks of territory from Boko Haram in Nigeria and al-Shabaab in Somalia (which had separate factions supporting ISIS and al-Qaeda), the groups extended their range of operations to neighboring countries, attacking military, government, and civilian targets. Rebels were also active, sometimes across borders, in Congo and Mali.
Asia
Green-on-blue attacks in Afghanistan were particularly popular in Afghanistan, where the ongoing insurgency continued into its 15th year. Bangladesh became a new region for attacks by IS-inspired terrorists, although the government tended to blame local groups vice external IS direction.
Europe
Attacks by ISIS in Europe included those ordered by operatives in Raqqa, the organization’s capital in Syria, as well as individuals or couples who attempted to increase body counts by resort to automatic weapons or simply driving vehicles into civilian crowds, showing again how terrorists alter their tactics to overcome government security measures to harden previous targets. Vehicular attacks were especially gruesome in Turkey, France, and Germany, along with shootings in Belgium. In addition to this expansion of the IS operational environment to Europe, also troubling was the arrest of a member of the German BfV intelligence organization who had offered to assist terrorists infiltrate the government.
North America
Law enforcement authorities shut down a score of would-be terrorist attacks, bringing many lone wolves, be they jihadis or right-wingers, to trial and prison sentences. However, the U.S. suffered its most deadly mass shooting when a lone jihadi killed 49 patrons of the Pulse nightclub in Florida.
Key Terrorists
In the 2013-2015 prequel to this volume, I suggested that terrorism-hunters concentrate on several key terrorists, including
- Abu Ali al-Anbari, IS deputy leader for Syria. He was killed in an airstrike—of uncertain provenance—in August 2016.
- Ibrahim Hassan al-Asiri, AQAP’s chief bomb maker
- Samantha Louise Lewthwaite, believed to be an al-Shabaab strategist
- Abubakar Shekau, Boko Haram leader.
- Ayman Mohammed Rabie al-Zawahiri, the al-Qaeda leader whose videos with limited production values offered minimal value to the next generation of jihadis.
- Returning jihadis from ISIS territory. Hundreds of terrorism tourists proved a difficult task for surveillance teams.
- Lone wolves. Many popped up throughout the rest of the world. Security forces stopped many, but not all, before they could attack.
The rest, so far, have survived. Some terrorists, including al-Asiri and Lewthwaite, vanished from view. Terrorists generally do not retire peacefully, usually either dying on the battlefield or in prison. The following did not get past the year:
Senior Terrorists Killed in 2016
This list includes those killed by coalition forces, including by airstrikes, and by rival terrorist groups, plus those who died of natural causes.
Al-Qaeda
- Rifai Ahmad Taha, a senior Egyptian member in Syria
AQAP
- Jalal Belaidi, alias Abu Hamza, a top AQAP commander who led AQAP in Zinjibar, Yemen
- Ali Abed al-Rab bin Talab, alias Abu Anwar, AQAP’s chief judge in Hadramawt Province, Yemen
ISIS
- Abu Mohammad al-Adnani, born Taha Sobhi Falaha, spokesman and possible successor to al-Baghdadi
- Khaled Afer, alias Abu Sarya, a close associate of IS spokesman Abu Mohammed al-Adnani, responsible for IS operations in Mosul
- Maher al-Bilawi, commander in Fallujah
- Basim Muhammad Ahmad Sultan al-Bajari, deputy minister of war
- Noureddine Chouchane, Tunisian ISIS leader believed key to plotting two attacks against tourists in Tunisia
- Salman Sahib Abd-al-Jabouri, variant Suleiman Abd Shabib al-Jabouri, alias Abu Saif, a member of the IS war council, who was responsible for attacks in Makhmour.
- Jasim Khadijah, former Iraqi officer connected to the March 19, 2016 rocket attack on Fire Base Bell that killed a USMC Staff Sergeant and wounded eight other U.S. soldiers
- Hafiz Sayed Khan, leader of IS in Afghanistan and Pakistan
- Abu Khatab, IS military commander for the Qaa border area in Lebanon
- Mohammed al-Maliki, Saudi IS member involved in several attacks in Saudi Arabia
- Assi Ali Mohammed Nasser al-Obeidi, senior ISIS military commander in western Iraq and eastern Syria
- Neil Prakash, 24, alias Abu Khaled al-Cambodi, Australian IS operative and propagandist
- Abd al-Rahman Mustafa al-Qaduli, alias Abu Alaa al-Afri, IS finance minister, believed by some to be the IS deputy chief
- Wael Adel Salman, alias Abu Muhammed Furqan, information minister and member of the Senior Shura Council
- Abu Omar Saraqib, military operations commander in Syria’s Aleppo Province
- Omar al-Shishani, alias Omar the Chechen, born Tarkhan Tayumurazovich Batirashvili in Georgia, USSR, IS minister of war
- Abu Hayjaa al-Tunsi, senior IS commander
- Abu Wahib, IS’s military emir in Iraq’s Anbar Province
Ansar Beit al-Maqdis
- Abu Doaa al-Ansari
Al-Nusra Front/Fatah al-Sham Front
- Ahmed Salama Mabrouk, alias Abu Farag al-Masri, a senior Egyptian commander close to Ayman al-Zawahiri
- Abu Firas al-Souri, spokesman
Al-Shabaab
- Mohamed Dulyadeyn, believed behind the April 2015 attack on Kenya’s Garissa University College that killed 147 people
- Mahad Mohammed Karate, al-Shabaab’s intelligence chief who also handled internal security
- Mohamed Mire, al-Shabaab’s governor for Somalia’s Hiran region and a key member of the group’s finance wing
- Yusuf Ali Ugas, regional commander, recruiter and influential preacher
Afghan Taliban
- Mullah Akhtar Mohammad Mansour, head of the Taliban
Pakistani Taliban
- Muhammad Ghauri, al-Qaeda activist and Pakistani Taliban member who was convicted of and executed by Pakistan for involvement in the 2009 attack on a Rawalpindi mosque that killed 38 worshippers
Boko Haram
- Abu Bakar Shekau, the group’s leader, who has been declared dead four times by various Nigerian officials. His status remained a mystery, as some observers suggested he used body doubles.
Hizballah
- Mustafa Badreddine, military commander involved in numerous terrorist attacks on Western interests in Lebanon
East Indonesian Mujahideen
- Abu Wardah Santoso, EIM’s leader
Jaish-e-Muhammad
- Saifullah, operations chief in India
Jamatul Mujahedeen Bangladesh
- Akash, the group’s leader
- Tamim Chowdhury, a Bangladeshi Canadian who fought in Syria for ISIS and who led JMB
Hizbul Mujahideen in Indian Kashmir
- Burhan Wani, chief of operations
Vilayat Caucasus
- Rustam Magomedovich Aselderov, alias Abu Muhammad, the group’s leader
Other Terrorists Killed in 2016
Algerian Armed Islamic Group and AQIM
- Mouloud Baal, alias El Moundhir
ISIS
- Sammy Djedou and Salah Gourmat, believed tied to the November 2015 Paris attacks and close associates of the late ISIS external operations leader Abu Mohammed al-Adnani
- Hatim Talib al-Hamduni, military commander in Mosul and head of military police for the self-proclaimed Ninawa state
- Walid Hamman, convicted in absentia in Belgium for a foiled 2015 attack
- Abu Jandal al-Kuwaiti, a senior military commander in Raqqa, Syria
- Omar al-Shishani, a military commander in Iraq and Syria
- Abu Sa’ad al-Sudani, a Sudanese IS fighter, and his wife, Australian Shadi Jabar Khalil Mohammad, sister of a 15-year-old who shot to death a police accountant in Sydney, Australia
Afghan Taliban
- Maulvi Noor Agha, shadow Sangin District chief in Helmand Province
- Qari Ghafour, a senior commander in Kunduz Province
- Mir Hamza, district leader in Grishk
- Mustaqeem, war commander in Helmand Province
- Mullah Abdul Rahim, shadow governor for Helmand Province
Boko Haram
- Abubakar Mubi, Malam Nuhu, and Malam Hamman, local commanders
Lashkar-e-Jangvi
- Qari Ajmal, wanted for an attack on the Sri Lankan cricket team in 2009 that killed six police and wounded seven players
Muslim Brotherhood of Egypt
- Mohammed Kamal, believed involved in more than a dozen armed attacks, including assassinations
- Yasser Shahata Ali Ragab, sentenced for assault and kidnapping
Key Terrorists Captured in 2016
Boko Haram
- Ansaru faction leader Usman Umar Abubakar, alias Khalid al-Barnawi
ISIS
- Sleiman Daoud al-Afari, head of the group’s chemical weapons research unit
This book uses the same definition of terrorism as found in its predecessors, allowing comparability across decades. Terrorism is the use or threat of use of violence by any individual or group for political purposes. The perpetrators may be functioning for or in opposition to established governmental authority. A key component of international terrorism is that its ramifications transcend national boundaries, and, in so doing, create an extended atmosphere of fear and anxiety. The effects of terrorism reach national and worldwide cultures as well as the lives of the people directly hurt by the terrorist acts. Violence becomes terrorism when the intention is to influence the attitudes and behavior of a target group beyond the immediate victims. Violence becomes terrorism when its location, the victims, or the mechanics of its resolution result in consequences and implications beyond the act or threat itself.
The book is divided into three sections: a region-by-region (and within each, a country-by-country) look at terrorist incidents, an index of groups and organizations mentioned in the incident descriptions, and a bibliography. As an innovation from earlier versions of this series, the locational sorting makes for easier use for the reader. The Incidents descriptions are based solely on publicly available sources. This section is not intended to be analytical, but rather comprehensive in scope. As such, the section also includes descriptions of non-international, and sometimes non-terrorist, attacks that provide the security and political context in which international attacks take place. In some cases, the international terrorists mimic the tactics of their stay-at-homecohorts. Often, these are the same terrorists working on their home soil against domestic, rather than foreign, targets. Domestic attacks often serve as proving grounds for techniques later adopted for international use. I have therefore included material on major technological, philosophical, or security advances, such as: the use of letter bombs; food tampering; major assassinations; attempts to develop, acquire, smuggled, or use precursors for an actual chemical, biological, radiological, or nuclear weapon; key domestic and international legislation and new security procedures; key arrests and trials of major figures; and incidents involving mass casualties.
The section also provides follow-up material to incidents first reported prior to January 1, 2016. Updates include information about the outcome of trials for terrorist acts occurring prior to 2016 and “where are they now” information about terrorists and their victims. The update is identified by the original incident date and offers enough description to give some context and to identify the original incident in the earlier volumes.
The international terrorist incidents and airline hijackings are identified by an eight-digit code. The first six digits identify the date on which the incident became known as a terrorist attack to someone other than the terrorists themselves (e.g., the date the letter bomb finally arrived at the recipient’s office, even though terrorists had mailed it weeks earlier; or the date on which investigators determined that a situation was attributable to terrorism). The final two digits ratchet the number of attacks that took place on that date. In instances in which either the day of the month or the month itself is unknown, “99” is used in that field. Non-international entries do not receive an eight-digit code.
The information cutoff date for this volume is December 31, 2016. If not otherwise specified, data comes from Associated Press coverage of the events.
The Bibliography section includes references drawn from the same public sources that provide the incidents, literature searches, and contributions sent by readers of previous volumes. It does not purport to be comprehensive. The citations are grouped into topic areas that were chosen to make the bibliography more accessible, and includes print and web-based material. The Bibliography gives citations on key events and may be referenced for more detail on specific attacks described in the Incidents section.
For those who prefer to run textual searches for specific groups, individuals, or incidents, a computer version of the 1960-2007 ITERATE (International Terrorism: Attributes of Terrorist Events) textual chronology is available from Vinyard Software, Inc., 502 Wandering Woods Way, Ponte Vedra, Florida 32081-0621, or e-mail via vinyardsoftware@hotmail.com The data set comes in a textual version and mimics the hardcopy chronologies. A numeric version offers circa 150 numeric variables describing the international attacks from 1968-2016. The data sets can be purchased by specific year of interest. See www.vinyardsoftware.com for further details.
Vinyard also offers the Data on Terrorist Suspects (DOTS) dataset, which features a detailed biographical index of every terrorist suspect named in the previous volumes of this chronology.
Comments about this volume’s utility and suggestions for improvements for its likely successors are welcome and can be sent to vinyardsoftware@hotmail.com. Please include your terrorism publication citations to ensure inclusion in the next edition of the bibliography.
Once again, there are many individuals who have contributed to this research effort. Of particular note are the staff at McFarland, who have a well-earned reputation for quality and for being exceptionally easy to work with; and my family.