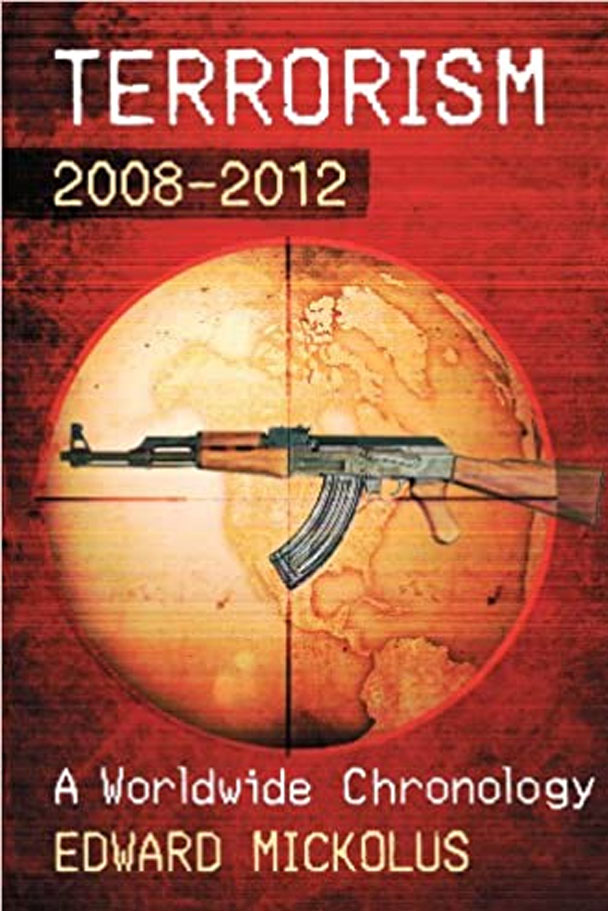
This comprehensive chronology provides coverage of every international terrorist attack covered in public literature–including newspapers, news magazines, radio, television, websites, and other media–from 2008 through 2012, plus updates on events that occurred before that period.
It notes trends in suicide bombings, violence against Western and local hostages, letter bombs, food tampering, major assassinations, and other attacks by terrorists of all stripes.
Changes in security measures around the world are also included, as are the key players in each event, ranging from terrorists to victims to individuals trying to prevent the next attack.
- Title : Terrorism, 2008-2012: A Worldwide Chronology
- Authors : Edward Mickolus
- Publisher : McFarland
- Publication Date : March 3, 2014
- Paperback : 344 pages
- ISBN-10 : 0786477636
- ISBN-13 : 978-0786477630
- Item Weight : 1.3 pounds
- Dimensions : 7 x 0.69 x 10 inches
Reviews
“A good source for quick, basic information on all types of terrorism. Recommended.” ―Choice
“This book would be the perfect gift for many politicians on both sides the aisle. The meticulous detail that Mickolus brings to the book is mind-numbing. This is a book not to be missed.” ―ARBA
“Meticulously researched…an indispensable reference work…. Highly recommended.” ―Reference Reviews.
Introduction
With the publication of this volume, I, singly or in tandem, have written some 20 volumes of chronologies and biographies of terrorists in the past 3+ decades. While I have hoped that each volume would be the last in the series, individuals willing to follow their fellow thugs into these pages continue to come forward.
Using a comprehensive definition, this chronology considers terrorism to be the use or threat of use of violence by any individual or group for political purposes. The perpetrators may be functioning for or in opposition to established governmental authority. A key component of international terrorism is that its ramifications transcend national boundaries, and, in so doing, create an extended atmosphere of fear and anxiety. The effects of terrorism reach national and worldwide cultures as well as the lives of the people directly hurt by the terrorist acts. Violence becomes terrorism when the intention is to influence the attitudes and behavior of a target group beyond the immediate victims. Violence becomes terrorism when its location, the victims, or the mechanics of its resolution result in consequences and implications beyond the act or threat itself.
The period of 2008-2012 saw the continuation of trends identified in previous years, although it also saw the failure of some long-held analytic predictions. Some predictions were made by pundits, who are paid for spouting opinions and issuing slogans masquerading as insight, not for developing understanding. But others were made by respected academics, who look at patterns from history, and might miss the “black swan” problem noted by Nassim Nicholas Taleb, such as the 9/11 attacks.
Most attacks continue to be low-level, unsophisticated bombings and shootings, with terrorists going after targets of opportunity rather than mounting complex operations that are the stuff of Hollywood movies and thriller novels. Some operations, most notably the three-day siege of Mumbai by jihadis in November 2008 and the takeover of an Algerian gas production facility that occurred at the time of this writing in January 2013, underscored for many that not all terrorists will opt for the easy hit, however.
Al Qaeda’s affiliates made kidnapping into a mobile murder method vice a mobile barricade-and-hostage method that it had been in the 1970s-1980s.
We can put to bed a myth about terrorist behavior that has become “common knowledge” amongst the commentariat. Although the media will swear on a stack of (insert your preferred religion’s preferred book here), there is no evidence for the assertion that terrorists conduct followup attacks on major dates, be it religious holidays, holidays for the target’s nationalities, feastdays of major terrorists, arrest dates of terrorists, or anniversaries of terrorist events. Al Qaeda has conducted no further attacks on, say, September 11 (anniversary of 9/11), July 7 (anniversary of the London subway attacks), March 11 (anniversary of the Madrid train attacks), etc. Pundits celebrate anniversary dates; terrorists do not. Terrorists know that the media will herald an upcoming date, and security services, heeding the counsel of their public affairs offices, will put on a display of preventive zeal. All for naught. Terrorists attack on the date that they believe will work now, not that worked in the past.
Much was made of the coincidental date of the attack on the US diplomatic facility in Benghazi, Libya on September 11, 2012 in which four US diplomats, including the US Ambassador, were murdered. With tens of thousands of terrorist attacks having been logged during the period covered by this chronology series, date overlap is unavoidable. It is noteworthy that although Islamists were credited with the attack, none of the groups claiming credit cited any link to the September 11, 2001 attacks. Moreover, there was no evidence of an involvement by al Qaeda per se.
Al Qaeda continued its transformation from a tightly controlled organization bowing to the whims of one individual to a loose confederation of like-minded jihadi zealots. On occasion, al Qaeda “Central”—the group immediately surrounding Usama bin Laden and Ayman al-Zawahiri, plus the al Qaeda operations chief of the day (they keep getting killed)—bequeaths associate status on a franchise and permits it to use the al Qaeda brand. Hence, the growth of al Qaeda in the Islamic Maghreb, al Qaeda in the Arabian Peninsula, and al Qaeda in Iraq. Although al Shabaab in Somalia has not adopted the al Qaeda name, it, too, seems have acquired second circle status. Other groups with close ties to al Qaeda, including Jemaah Islamiyah in Indonesia and Abu Sayyaf in the Philippines, have yet (at least, as of this writing) to obtain formal franchise status. Similarly, despite the similarity of their stated goals and interconnections of its membership, al Qaeda has not included the Chechens, Islamic Movement of Uzbekistan, or Uighurs as formal franchise spinoffs. Still other wannabes travel to the caves and training centers of al Qaeda to seek weapons, training, and the blessing of the core group.
Among theses wannabes has been a disturbing number of American citizens, many of them Western-looking and American–accented radicals steeped in US culture and able to move more easily in the American environment. While excellent law enforcement work has led to the arrests and imprisonment of dozens of these individuals, it is clear that al Qaeda continues to believe that the Westernization of its operational cadre offers opportunities for attacks on the “far enemy”—the US homeland.
What to do with terrorists plagued the Bush and Obama administrations during this period. Media upset over interrogation methods and incarceration procedures led to calls for a catch-and-release policy, changes to questioning methods (on the dubious proposition that terrorists would commit themselves to similar limitations on their handling of hostages), and a shift to kinetic responses. Airstrikes took out many leaders of al Qaeda central and its affiliates in Yemen, while scores of others were released from Guantanamo Bay military prison; still others awaited trial, as judicial scholars and others pondered whether military or civilian courts were the more appropriate fora. Several of those passed on to their home governments and ultimately locally declared no longer a threat soon became leaders of terrorist organizations, with membership in the Gitmo alumni association giving instant street credibility among their brethren.
Aspects of the detainees’ defenses continued to divert media attention. Many of the Guantanamo detainees claimed, in essence, that their training in al Qaeda camps in then-Taliban-governed Afghanistan were mere praycations, not terrorist-related. Others, most notably the “high value” detainees such as Khalid Sheikh Muhammad, al-Hawsawi, and Ramzi bin-al-Shibh attempted to make their hearings an opportunity to spout their propaganda rather than offer true defenses for their actions.
Governments wrestled with the juridical treatment of the prosecutable and perhaps non-prosecutable detainees as well as alumni of prisons. Countries tried various solutions, with differing amounts of legislative, oversight, domestic public, international, and legal support.
The US explored sending many Guantanamo Bay detainees to willing countries, and substantially reduced its prison population. The merits of military commissions and civilian criminal trials were weighed, and sometimes tried in test cases. Ahmed Ghailani, accused in the August 7, 1998 bombing of US Embassies in Kenya and Tanzania, narrowly missed a not guilty verdict on all 285 charges, being convicted of only a single charge of conspiracy in a civilian criminal court. “Not in my backyard” was the frequent lament of officials of cities on the short list of possible court fora for other trials of high value detainees.
Various civil rights and human rights groups spent more time worrying about the treatment of those charged—and sometimes not yet charged—with terrorism than with the effects on the victims, and diverted resources of governments battling terrorist predators. The American Civil Liberties Union challenged the US administration’s dead-or-alive order for Anwar al-Aulaqi, who was connected to the perpetrators of several foiled and successful attacks and believed by many to be Al Qaeda in the Arabian Peninsula’s inspirational successor to Osama bin Laden. Rather than spend up to $80 million in litigation expenses and tying up the time of investigators defending against charges of undue interrogation methods, the British government agreed to an out-of-court financial settlement with 15 Guantanamo Bay former detainees and one still incarcerated. A Polish government agency declared “victim” status for Abd-al-Rahim al-Nashiri, a high-value al Qaeda detainee.
Law enforcement and intelligence officers continued their stunning record of successes against terrorist threats. While there were several near-misses, and, unfortunately, some successes by terrorists, on the whole, the period was one of few actual attacks on the US homeland. It was not for lack of trying by the terrorists.
This record of success was easy for the media to ignore, as a streak of luck, particularly with the failed December 25, 2009 underwear bombing and the May 1, 2010 Times Square fizzle, underscored that terrorists only need one win, and have a different view of what constitutes success. Self-appointed terrorism experts within the media’s punditocracy bloviated about “connecting the dots”, as if the exceptionally intricate work of terrorism analysis merits reduction to such simplistic sloganeering. Piecing together tidbits post facto to fit a predetermined argument is easy. Figuring out what’s going on when you’re trying to monitor more than half a million names (which appear in several federal databases) in a tsunami of data and vet often conflicting threat information is another matter. The commentariat never provides any ideas on precisely what should be changed. Non-accountable amateur blognoscenti saying ex cathedra “connect the dots”, “be creative”, “get more and better intelligence,” “all we need is better humint,” “just penetrate them,” “collaborate,” etc., without offering specifics is hardly illuminating uncharted, heretofore unconsidered territory. But the search for blame is easier than the discovery of effective antiterrorist methods.
The drawdown of US and coalition forces in Iraq and (as of this writing) planned drawdown in Afghanistan has come at a time when terrorist attacks are on a downward glide in Iraq, but an upward path in Afghanistan. Many observers wonder whether the comparative quiet in Iraq will continue when the local security services are on their own against the terrorists. Very preliminary evidence suggests that the terrorists won’t go away quietly. Al Qaeda in particular continued its expansion to new regions, with the successor to an Algerian Islamist group taking the name of Al Qaeda in the Islamic Maghreb and took over a slice of Mali the size of Texas. Al Qaeda in Iraq sponsored the growth of the al Nusrah Front, an Islamist rebel group that expanded operations during the seemingly unending Syrian civil war. Meanwhile, an al Qaeda-like group, Boko Haram, was responsible for hundreds of murders in northern Nigeria, specializing in multiple-casualty bombings of churches and attacks on government facilities. The Taliban in Afghanistan and Pakistan continued their depredations, while al Qaeda in Iraq exploited security gaps. Despite airstrike attacks that decimated al Qaeda Central leadership and drew down the leadership of al Qaeda in the Arabian Peninsula, plus the reversal of fortunes of al Shabaab in Somalia, the overall movement continued to pose major threats in their regions. Al Shabaab sympathizers attacked targets in Kenya while backing away from its earlier redoubts in Mogadishu. Most observers cited AQAP as the most likely to attempt to conduct attacks on the US homeland, while individual homegrown radicalized Islamists continued to be stymied by excellent work by the FBI. Increases in the treasury of AQIM thanks to acquiring millions from ransom payments for Western hostages, as well as smuggling operations, increased the operational potential of al Qaeda.
The major event in the ongoing al Qaeda narrative was the death of Usama bin Laden in a daring SEAL Team Six raid on his compound in Abbotabad, Pakistan on May 2, 2011. An exultant US administration also celebrated the killing in August 2011 of al Qaeda in the Arabian Peninsula operations chief Anwar al-Aulaqi. These deaths, and several more attributed to drone strikes, siphoned the strength of al Qaeda’s central leadership and that of its most operationally active affiliate, but was accompanied by much second-guessing from the sidelines. An embarrassed Pakistani government complained about a violation of sovereignty, while civil libertarians questioned whether there are detailed rules for determining when an American citizen can be targeted overseas.
Bin Laden’s successor, Ayman al-Zawahiri, peppers the Internet with commentary on a host of issues, some related to al Qaeda’s raison d’etre, some a mere attempt to appear relevant—or at least offer a proof of life—as jihadis continue to operate increasingly independently of the original al Qaeda. Al-Zawahiri’s ascension posed new issues for the organization, as his management style was viewed by some as abrupt, and the propaganda shop lamented a charisma gap between him and his predecessor. Al Qaeda affiliates were slow to pledge bayat—personal loyalty—to al-Zawahiri. Air strikes severely limited the group’s succession planning, as a litany of Zawahiri deputies were killed off.
One al Qaeda franchise that was especially active was its Arabian Peninsula group, operating out of the lawless areas of Yemen, with some spillover amongst radical Saudis. Anwar al-Aulaqi, with excellent knowledge of American culture, conducted propaganda operations aimed at recruiting Americans, to some success, contacting others, and inspiring still others to attack. Some observers worried that he would elbow even Osama bin Laden out as the major Islamist terrorist leader in the coming years. His simple message—try anything, you don’t need our approval—portended a terrorist movement far more difficult to penetrate, with no central command calling the shots. Although al-Aulaqi’s death took out a major spokesman for the al-Qaeda cause, many lone wolves, including Americans, continue to pop up, cherishing al-Aulaqi’s message of going it alone.
Tectonic change in the Middle East during the Arab Spring of 2011 sidelined al Qaeda to mere jeerleaders, calling for continued efforts against corrupt leaders. The overthrow of several regimes, including the violent overthrow of Mu’ammar al-Qadhafi in Libya, left al Qaeda without a say in the direction of the new Middle East. Al-Qadhafi’s death also removed a leading figure in the history of state sponsorship of terrorism. As time went on, however, jihadis with and without direct al Qaeda ties found ways to exploit the continuing instability in the region, seem in particular as a diminution of security service capabilities. Some services were more sympathetic to the jihadis’ goals, if not their methods, than their authoritarian predecessors. Some felt constrained to rein in their public cooperation with the US and other Western services out of concern for anti-Western “street” opinion. Still others have yet to achieve the levels of professionalism of their predecessors.
AQIM’s inroads in Mali, and fears of likely AQIM expansion of its territory leading to a takeover of the rest of Mali, led Paris to give up its wait for a promised West African military response to the crisis and in January 2013 initiate a military intervention to roll back AQIM. The millions of dollars in hostage ransoms, and the huge territorial expanse available, led many to worry that AQIM could give like-minded jihadis a safe haven and training opportunities rivaling those of the Taliban-era Afghanistan. AQIM’s imposition of an especially harsh interpretation of sharia, featuring destruction of holy sites and amputations, made the French action popular amongst the local population.
Terrorists continue to use the Internet in ways not initially conceived by security services. Trends identified earlier in this series—particularly with regards to its use in propaganda and clandestine messaging—have expanded. Increased use of blogs in Internet culture has been mimicked by terrorists, who now sport online magazines. The al Qaeda in the Arabia Peninsula Inspire, written in part by American al Qaeda members, has been a vanguard in the attempt to get Western kids hooked on the jihad by using cultural references.
While the al Qaeda diaspora gets the bulk of media attention, non-jihadi terrorists have not given up. The Revolutionary Armed Forces of Colombia, thanks to assistance from the neighboring government of Venezuela, leads the Latin American leftist cadres for longevity and audacity, while the Basque Nation and Liberty, despite arrests of its leaders on both sides of the French-Spanish border, garners headlines as one of Europe’s longterm terrorist groups. Even splinters of the Irish Republican Army and like-minded affiliates have continued conducting occasional operations. FARC was not without its difficulties, however, losing several senior leaders plus sustaining an embarrassing rescue operation of longtime hostage former Presidential candidate Ingrid Betancourt via government trickery. ETA unilaterally called another ceasefire in 2011. Hamas and Hizballah, while maintaining terrorist operational capabilities, have learned that the responsibilities of governance put them in a different phase of organizational development from that of simple revolutionary rhetoric and bomb-throwing. Lone wolves on the right also appear, most notably in Norway, where Anders Breivik’s bombing and shooting spree in July 2011 killed 68 people, mostly teens. The Breivik case also raises the issue as to whether lone wolves should be classified and treated as insane, or political terrorist groups with a membership of one.
The current volume follows that same format and method as the previous ones. As in earlier volumes, the international terrorist incidents and airline hijackings are identified by an eight-digit code. The first six digits identify the date on which the incident became known as a terrorist attack to someone other than the terrorists themselves (e.g., the date the letter bomb finally arrived at the recipient’s office, even though terrorists had mailed it weeks earlier; or the date on which investigators determined that an anomalous situation was terrorist in nature). The final two digits ratchet the number of attacks that took place on that date. On dates in which multiple attacks occurred in the same location, a dash is followed by the number of the last event in the series. For example, three attacks in the same location on the same date would be noted as XXXXXX01-03. In instances in which either the day of the month or the month itself is unknown, “99” is used in that field.
The book is divided into three sections: Incidents, Updates, and Bibliography. The Incidents section provides a chronology and description of international terrorist activity for a given time period, based solely on publicly available sources. This series of chronologies is not intended to be analytical, but rather comprehensive in scope. As such, the Incidents section also includes descriptions of non-international attacks that provide the security and political context in which international attacks take place. In some cases, the international terrorists mimic the tactics of their stay-at-homecohorts. Often, these are the same terrorists working on their home soil against domestic, rather than foreign, targets. Domestic attacks often serve as proving grounds for techniques later adopted for international use. I have therefore included material on major technological, philosophical, or security advances, such as: the use of letter bombs; food tampering; major assassinations; attempts to develop, acquire, smuggled, or use precursors for an actual chemical, biological, radiological, or nuclear weapon; key domestic and international legislation and new security procedures; key arrests and trials of major figures; and incidents involving mass casualties. Non-international entries do not receive an eight-digit code.
The Updates section provides follow-up material to incidents first reported prior to January 1, 2008. For example, updates include information about the outcome of trials for terrorist acts occurring prior to 2008 and “where are they now” information about terrorists and their victims. The update is identified by the original incident date, and I have included enough prefatory material to give some context and to identify the original incident in the earlier volumes.
The information cutoff date for this volume is December 31, 2012.
The Bibliography section includes references drawn from the same public sources that provide the incidents, literature searches, and contributions sent by readers of previous volumes. It does not purport to be comprehensive. The citations are grouped into topic areas that were chosen to make the bibliography more accessible, and includes print and web-based material. The Bibliography gives citations on key events and may be referenced for more detail on specific attacks described in the Incidents section. This volume’s bibliography includes a section on the research that has grown from the ITERATE (International Terrorism: Attributes of Terrorist Events) dataset, which is based upon these published chronologies.
For those who prefer to run textual searches for specific groups, individuals, or incidents, a computer version of the 1960-2007 chronology is available from Vinyard Software, Inc., 2305 Sandburg Street, Dunn Loring, Virginia, 22027-1124, or e-mail via vinyardsoftware@hotmail.com The data set comes in a WordPerfect and Word textual version and looks remarkably like the volumes in this series of hardcopy chronologies. A numeric version offers circa 150 numeric variables describing the international attacks from 1968-2012. The data sets can be purchased by specific year of interest. See www.vinyardsoftware.com for further details.
Vinyard also offers the Data on Terrorist Suspects (DOTS) project, where you will find a detailed biographical index of every terrorist suspect named in the previous volumes of this chronology.
Comments about this volume’s utility and suggestions for improvements for its likely successors are welcome and can be sent to me via vinyardsoftware@hotmail.com. Please send your terrorism publication citations to me at Vinyard to ensure inclusion in the next edition of the bibliography.
Once again, there are many individuals who have contributed to this research effort. Of particular note are Susan Simmons, who edited this volume; the staff at McFarland, who have a well-earned reputation for quality and for being exceptionally easy to work with; and my family, who once again wondered if there was still a dining room table buried underneath the files used to produce this work.